AccessPatrol USB DLP Software Overview (Video)

🆕 🔒 AccessPatrol USB Device Control Software—Block USBs, Track Data Transfers, and Stop Data Theft (2023)
AccessPatrol’s USB DLP Activity Dashboards Video (2022)
Hey everyone, this is Dale here. I am the Digital Marketing Manager for CurrentWare.
In today’s video, I’d like to show off the new USB activity dashboards introduced to AccessPatrol in version 7.0.
These dashboards provide a convenient overview of the peripheral device usage of your entire workforce as well as specific groups or users—all from the convenience of a web browser.
They work in tandem with AccessPatrol’s device control features and USB activity reports to protect sensitive data against the security risks of portable storage devices.
Today’s video is just a sneak peek of what AccessPatrol is capable of; as time goes on you can expect to see further enhancements and data points added to these dashboards.
What You Can Track With AccessPatrol USB DLP Software
At this time, AccessPatrol can track activities from the following peripherals:
- Portable storage devices such as USB flash drives, external hard drives, optical discs, tape drives, and SD cards
- and Mobile devices including smartphones, PDAs, and tablets
This device usage data is used to populate various graphs across AccessPatrol’s dashboards. You can further refine how granular this data is by limiting the time frame, selecting only specific groups, and even investigating individual users.
Having these metrics available at a glance makes detecting potential insider threats far more efficient as your organization scales.
Any groups or users that need to be reviewed further can be investigated using the more granular dashboards and AccessPatrol’s device activity reports.
For a more proactive approach to insider threat management you can set up targeted alerts that will notify designated staff members when these high-risk activities occur.
For the most up-to-date information on AccessPatrol’s activity tracking and data loss prevention capabilities, visit our knowledge base at CurrentWare.com/Support or visit the AccessPatrol product page at CurrentWare.com/AccessPatrol
Overview Dashboard
In the overview dashboard you can review the following metrics:
- File Operations that happened over the selected time period, including the number of files that have been copied/created, the number of files that have been deleted, and the number of files that have been renamed/saved as.
- Overall Device Activities, with a breakdown of how many of the peripherals were authorized and how many were blocked from use.
- The Top 5 File Types graph shows the most common file types that are copied/created or deleted to and from portable storage devices
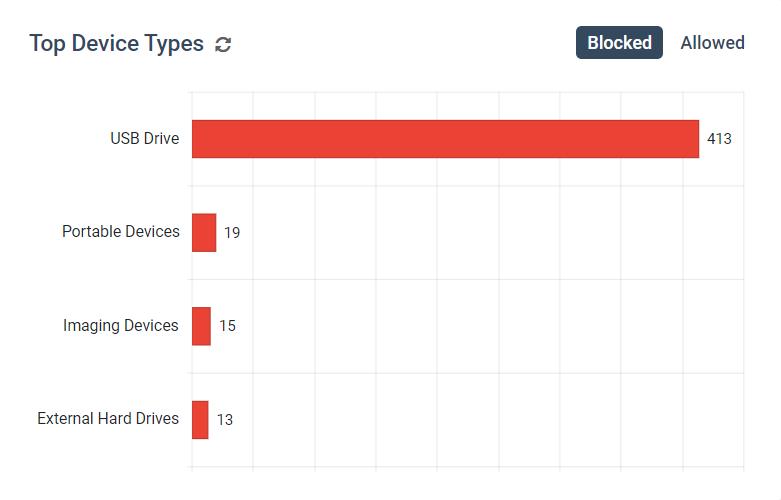
- The Top 5 Device Types graph shows the most common classes of peripheral devices that are blocked and allowed
- The Top 5 Files Operations graph shows which groups or users have the greatest number of files that have been Copied/Created and Deleted to and from portable storage devices
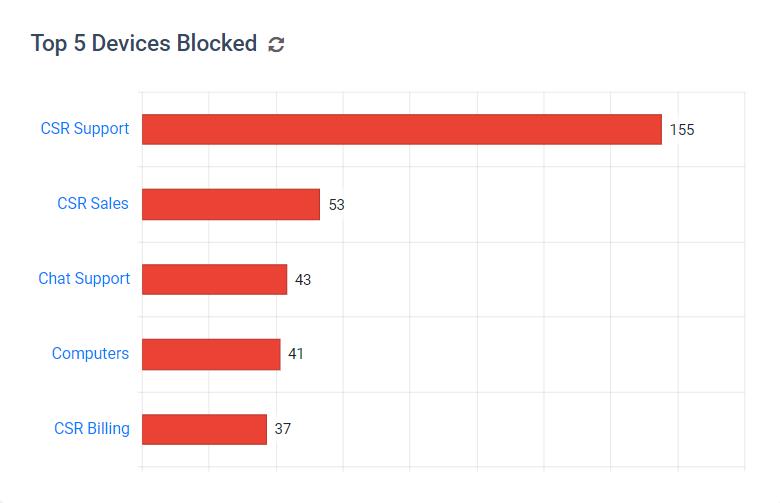
- The Top 5 Devices Activities graph shows which groups or users have the greatest number of Blocked and Allowed devices.
- And finally, The Activity Log provides access to the raw data, with controls to show and hide certain columns, filter and sort data, conduct searches, and export the data to an Excel spreadsheet or PDF. Each dashboard has their own Activity Log with columns that are relevant to that specific dashboard.
Files Dashboard
Moving on to the Files Dashboard you will see…
- A timeline of file operations that shows the relationship between the various operations over the course of the selected time period. This can be used to search for patterns in anomalous device usage, such as peaks in file transfers outside of regular operating hours.
- You will also see graphs with the Top File Types Copied/Created to internal hard drives and external devices
- Below that, we have graphs that show the users or groups that have Copied/Created or Deleted the most files
- And, just like the overview dashboard, there is an Activity Log with the raw data.
Devices Dashboard
Finally, we have the Devices Dashboard.
In this dashboard, we have…
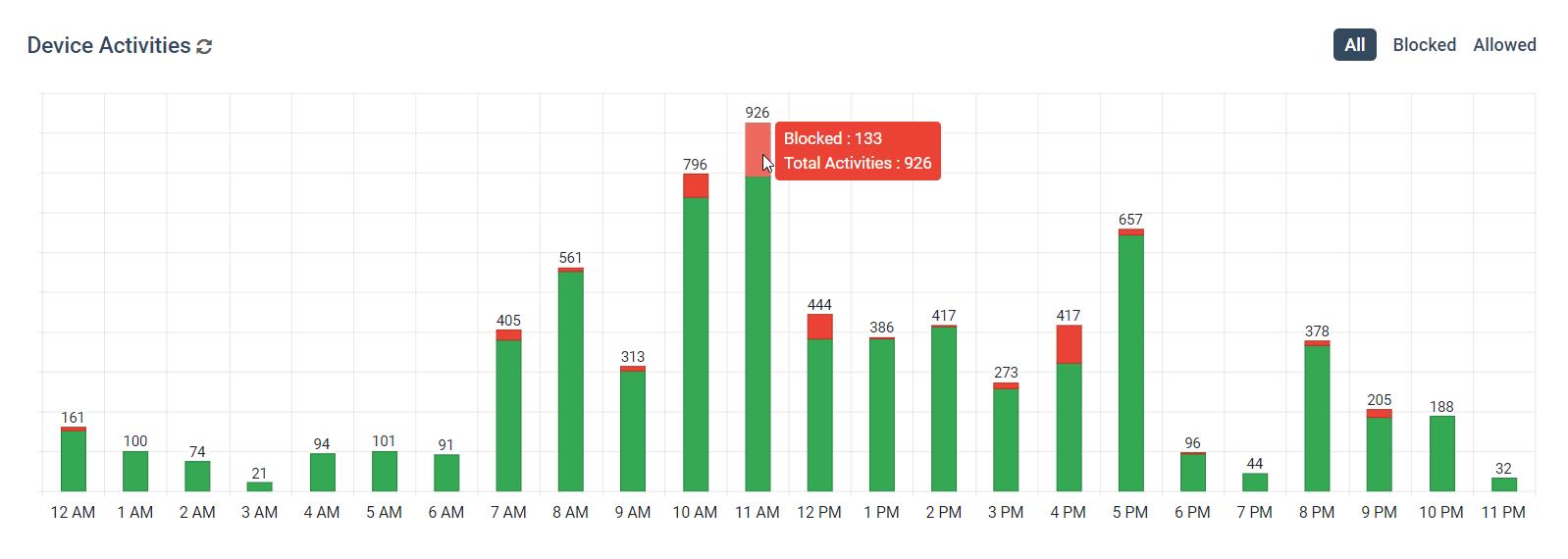
- A device activities graph that shows a timeline with the number of allowed and blocked devices each day. This can be further refined to show an hourly breakdown of a specific day so you can find out what time your users were attempting to use blocked devices.
- Next, we have graphs with the users or groups that have the most allowed and blocked devices activity over the selected time period.
- Scrolling down to the Activity Log, we can use the sorting controls to take a closer look at the users that have been attempting to use unauthorized peripherals.
AccessPatrol Use Case Demo: Investigating Insider Threats
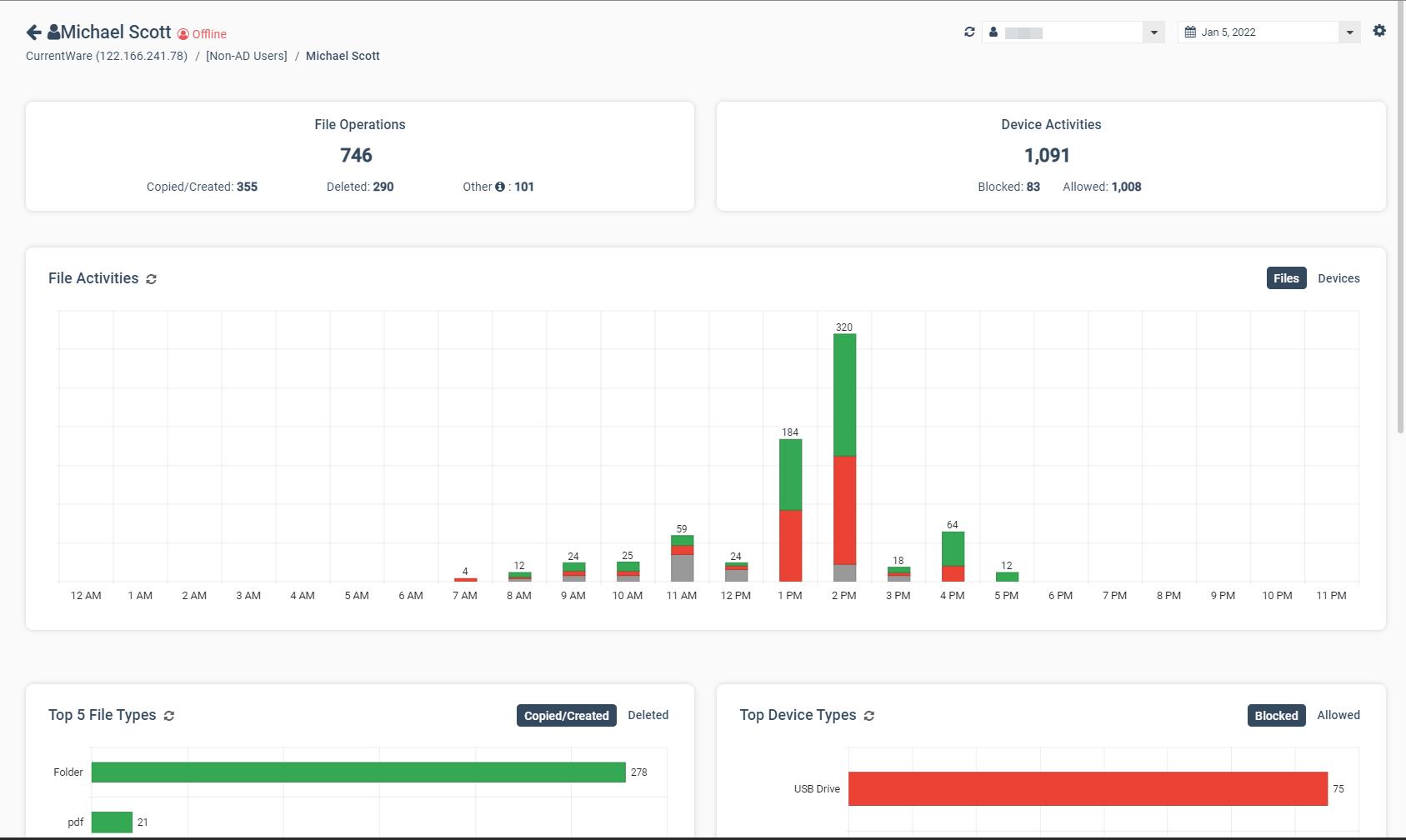
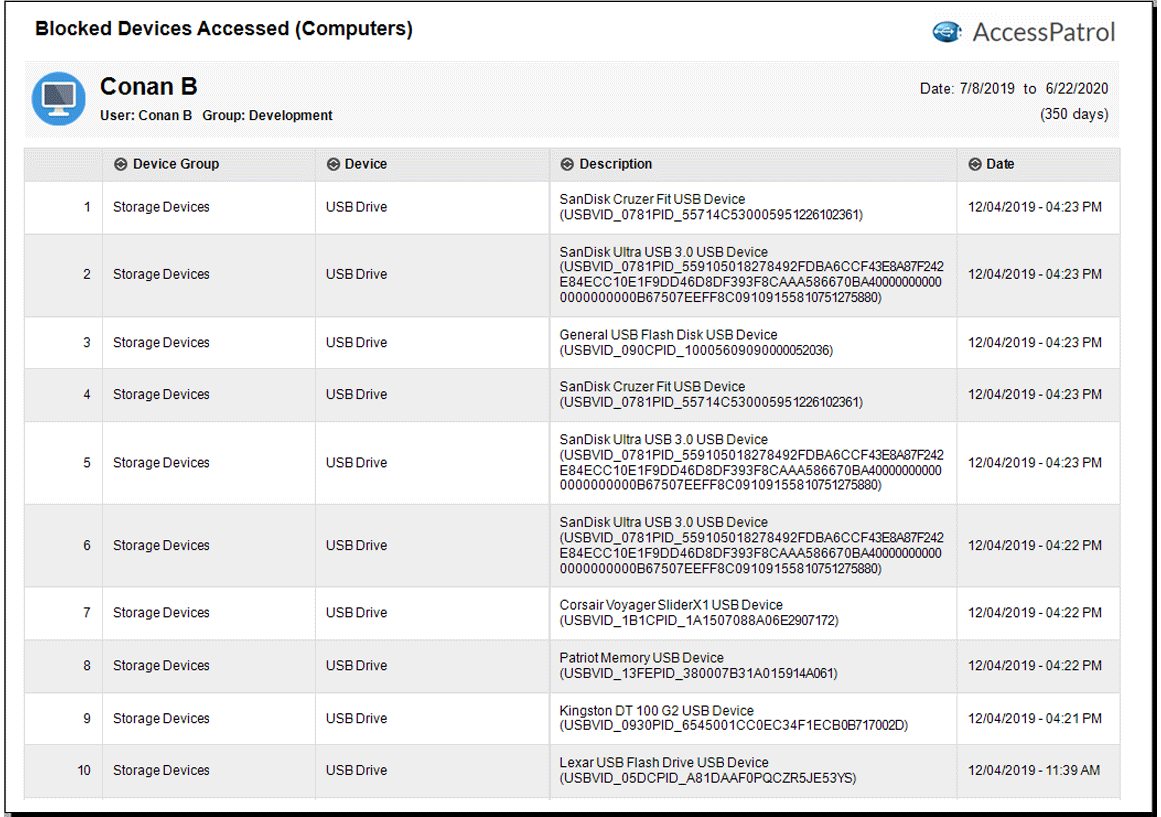
As you can see, we have specific users that are repeatedly trying to use devices that have not been approved for use by the organization.
While this could just be an accidental oversight on the user’s part, there’s a risk that it’s something much more serious.
For example, what if this is actually a disgruntled employee trying to steal trade secrets or sensitive customer data so they can bring it to a competitor, or worse, sell it to cybercriminals on the dark web.
Between the costs associated with a damaged reputation, fines, loss of competitive advantage, and remediation, a data breach like this could completely ruin a company.
Before we confront this employee or send them for retraining, let’s investigate this incident further so we can make an informed decision.
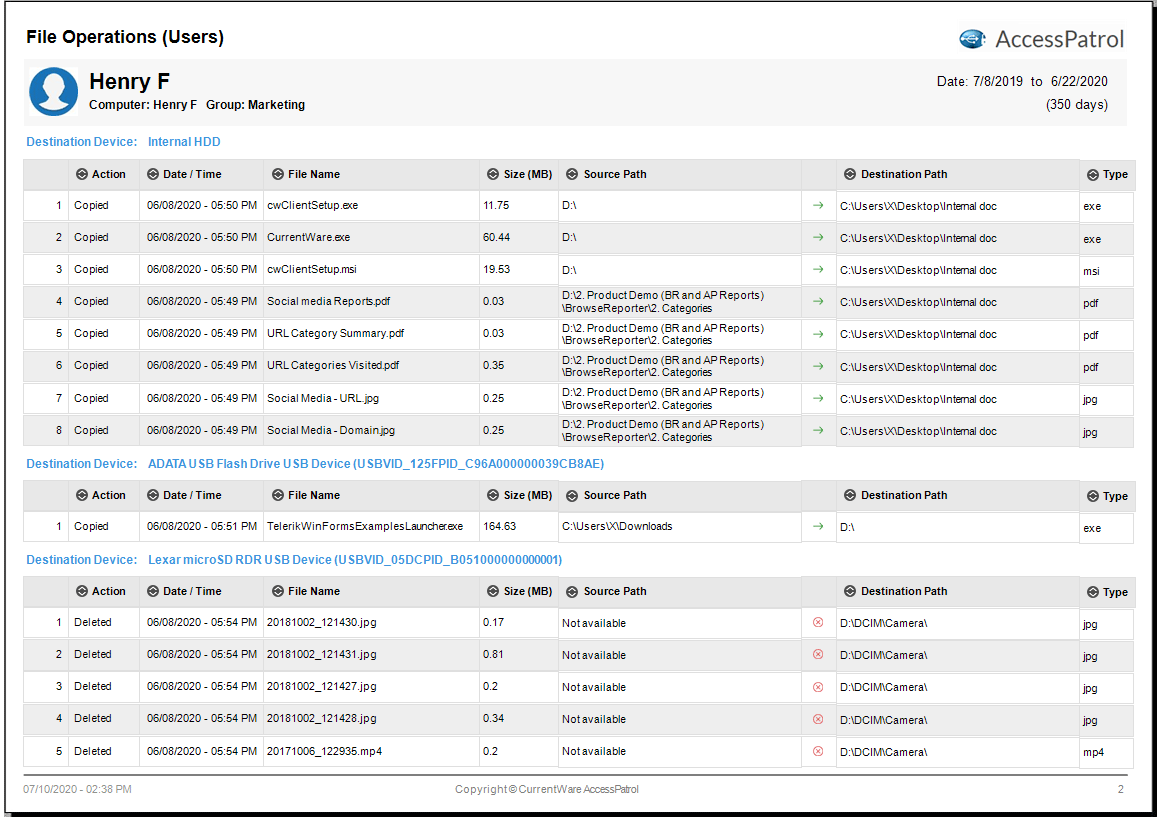
Clicking on this user, we’ll be taken to a dashboard that focuses exclusively on their activity.
Looking at the Devices graph we can see that they have made multiple attempts to use blocked devices.
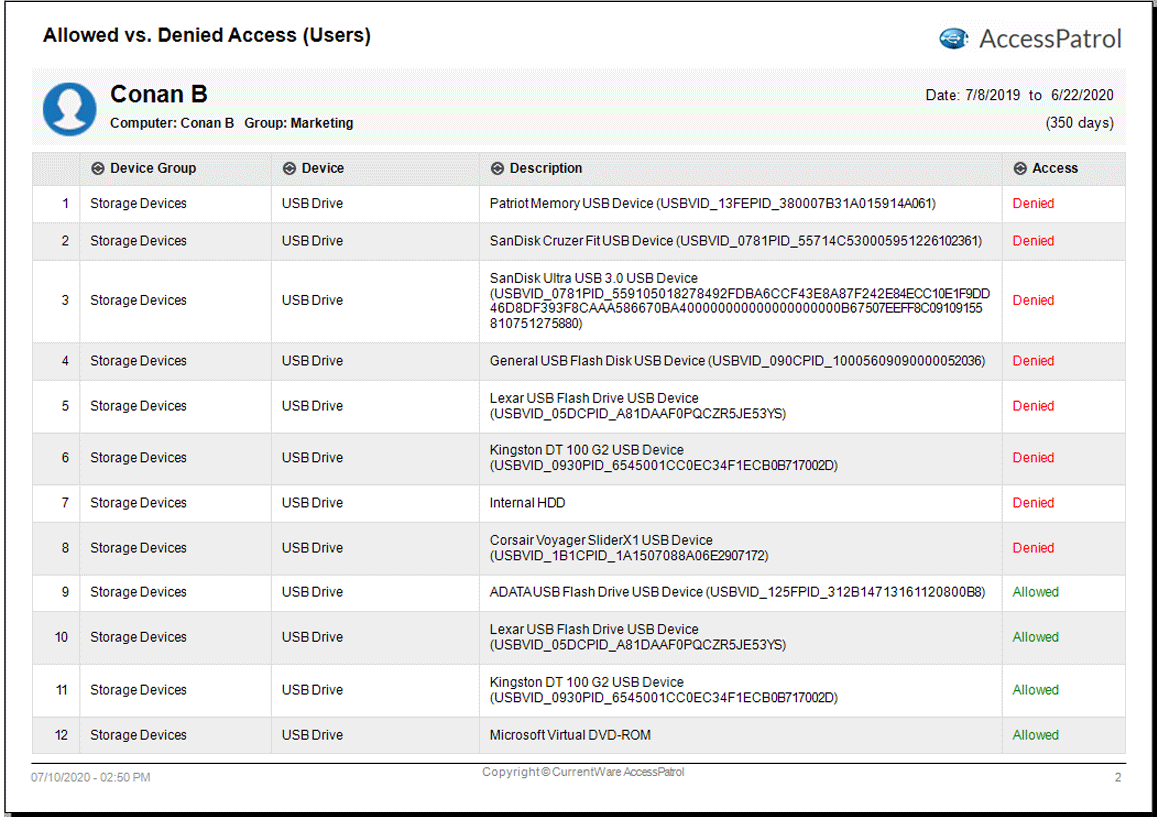
Scrolling down, we can see that they’ve been trying to use unauthorized portable storage devices.
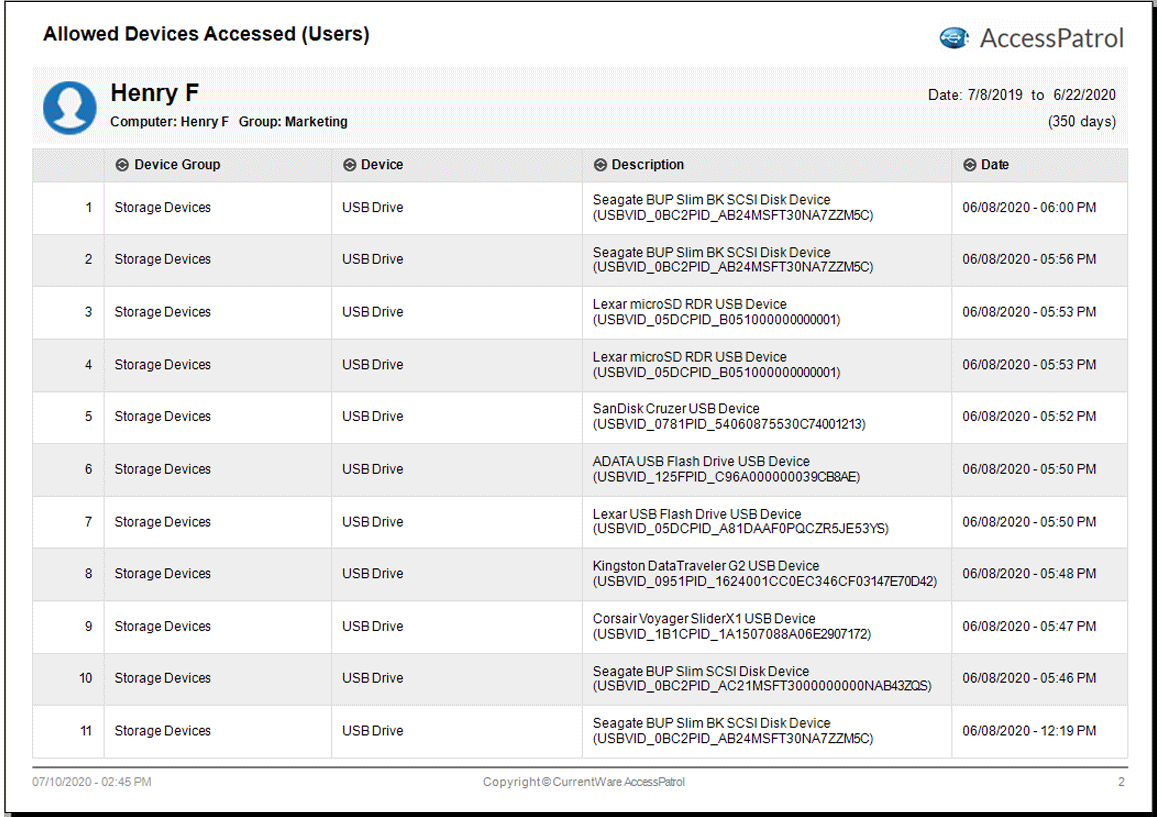
Since AccessPatrol is currently blocking any devices that are not explicitly allowed, I know that the only way sensitive data is leaving through a USB drive is if it’s a device that we’ve allowed before. So, let’s take a closer look at how they’ve been using their approved devices.
As you can see here, the types of files that they are transferring are more than capable of containing sensitive data; let’s take a look at the file names for more details.
With the Activity Log we can use the filters, sorting, and column options to isolate our view to the entries we’re the most interested in.
Once we find something that looks off, we have more than enough information to confront this employee and take any necessary corrective actions.
Outro
Ready to protect your sensitive data against theft to USB portable storage devices? Block and monitor peripheral device usage today with a free trial of AccessPatrol, CurrentWare’s USB control software.
Simply visit CurrentWare.com/Download to get started instantly, or get in touch with us at CurrentWare.com/Contact to book a demo with one of our team members. See you next time!
AccessPatrol Full Walkthrough Video
Video Transcript
AccessPatrol is a USB DLP device control software solution that protects sensitive data against theft to portable storage devices.
AccessPatrol keeps data secure by…
- Preventing users from stealing data or transferring malicious files with easily concealed USB flash drives
- Maintaining auditable records of file transfers to portable storage devices, and…
- Triggering real-time alerts when security policies are violated
AccessPatrol’s central console allows you to apply USB DLP security policies and run reports on your user’s USB activities from the convenience of a web browser.
The security policies are enforced by a software agent that is installed on your user’s computers. This keeps devices restricted and monitored even when the computers are taken off of the network.
USB DLP Features
Here’s an overview of AccessPatrol’s key USB data loss prevention features.
USB Device Control
Under Device Permissions, you can assign unique device control policies for specific groups of computers or users.
AccessPatrol controls a variety of peripherals, including…
- Storage devices such as USB flash drives and external hard drives
- Wireless Devices such as Bluetooth, Infrared, and WiFi
- Communication Ports such as Serial and Parallel ports
- Imaging Devices such as Scanners or Cameras, and…
- Other Devices such as network share drives, printers, and mobile phones
Under the allowed list you can specify trusted devices that can be used on your computers.
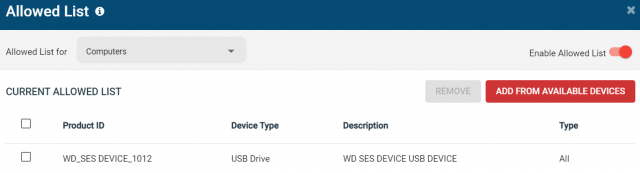
If you need to temporarily lift device restrictions for devices that aren’t on the allowed list, you can use the access code generator.
This allows you to set a time-limited policy exemption for a specific computer. The access code generator does not require internet access to work, making it the ideal solution for traveling users and other special circumstances.
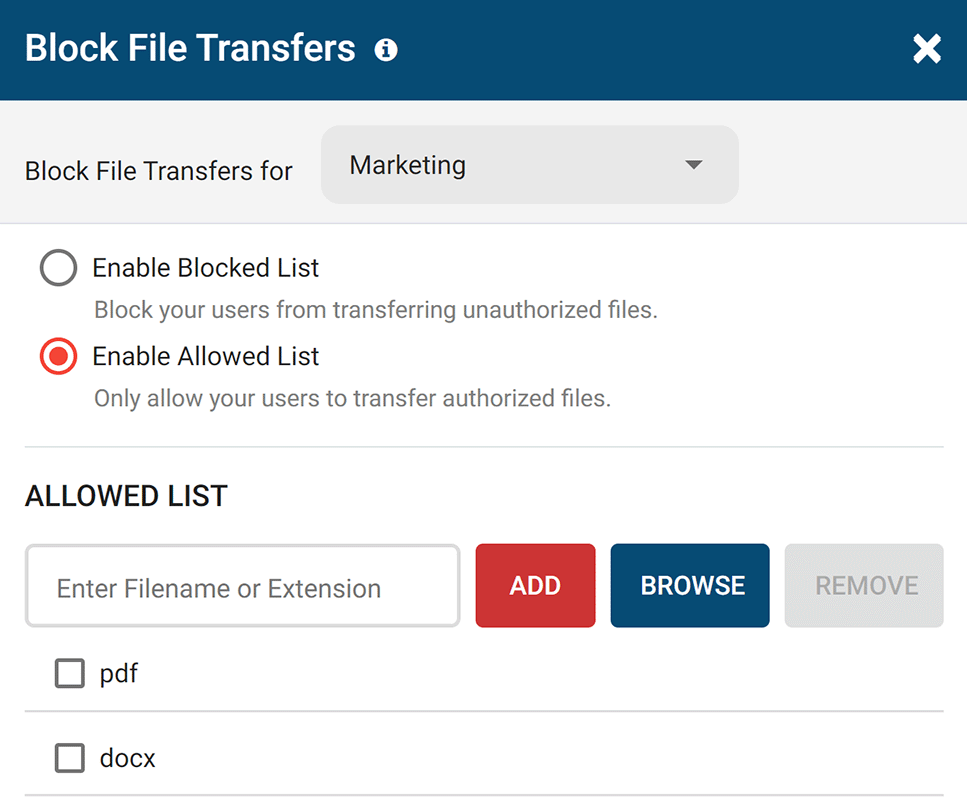
To further protect sensitive data, AccessPatrol allows you to block file transfers based on file names and extensions. This ensures that even allowed devices can’t transfer sensitive data.
USB Device Auditing and Monitoring Reports
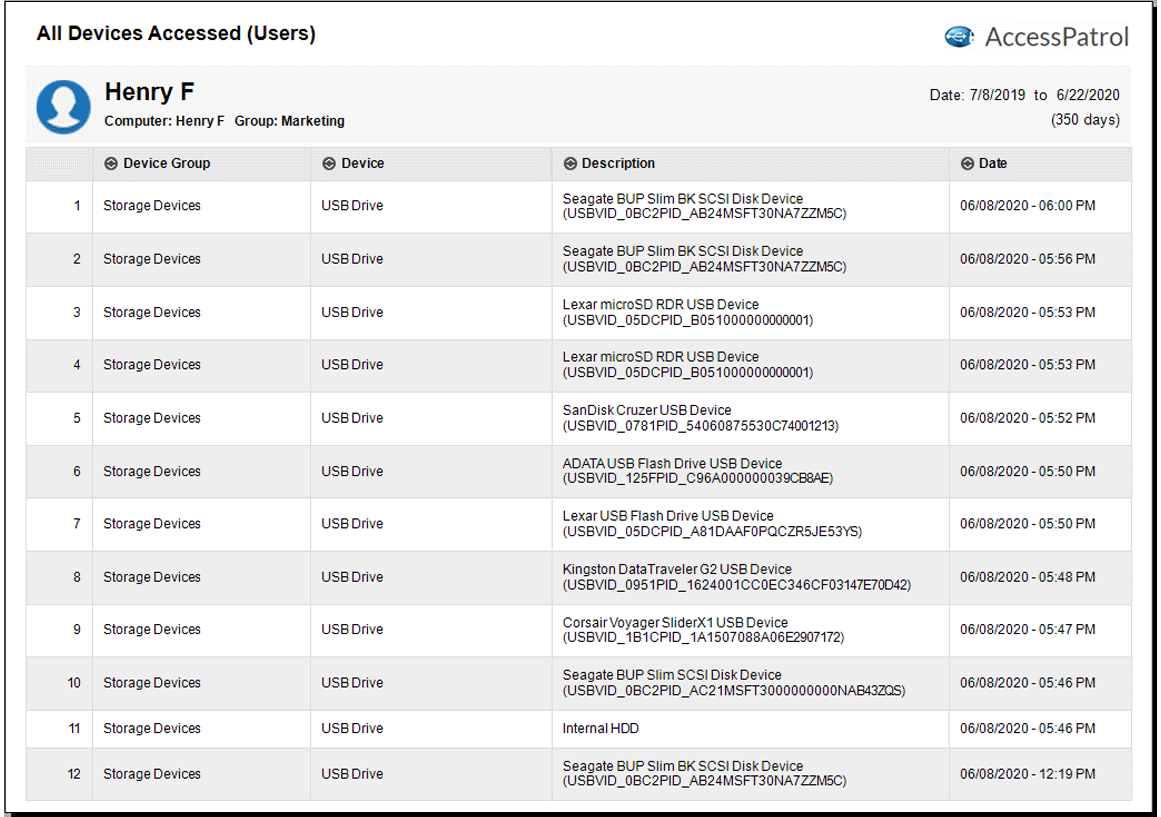
AccessPatrol also includes a variety of USB activity reports to help organizations audit data transfers and peripheral device use.
These reports provide insight into…
- All files that have been copied, created, renamed, or deleted on USB storage devices, and…
- A timestamped device history for each user, including attempts to use blocked devices
AccessPatrol’s reports can be generated on-demand, on a set schedule, or automatically sent to your inbox to alert you of specific events.
Conclusion
Don’t let a preventable data leak ruin your organization. Take back control over portable storage devices with a free trial of AccessPatrol.
Get started today by visiting CurrentWare.com/Download
If you have any questions during your evaluation our technical support team is available to help you over a phone call, live chat, or email.
Thank you!